https://www.europesays.com/2115558/ Top cities, dates to save #affiliate #Airbnb #cost #deloitte #Economy #Europe #Explainer #guides #last #local #LocalAffiliateTravel #London #low #LowCostU0026LastMinuteTravel #minūtē #Modular #ModularStory #neutral #not #Overall #OverallNeutral #Rome #story #summer #Tokyo #transportation #travel #TravelGuidesU0026Travelogues #TravelU0026Transportation #Travelogues #TTP #TTPExplainerNotVisual #u0026 #UK #Vacation #VacationTravel #visual
Recent searches
Search options
#ttp
Ever feel like the universe is talking directly to YOU? This #relatable moment from #TheTalosPrinciple hits HARD. Are the devs spying on us?
Watch and tell me I'm not alone!
Pacers vs Knicks NBA playoffs history: Top moments from rivalry https://www.rawchili.com/nba/39313/ #Basketball #Indiana #IndianaPacers #Knicks #Listicle #National #NationalSports #NBA #NBAPlayoffs #new #NewYorkKnicks #News #Overall #OverallPositive #Pacers #playoffs #Positive #Sports #SportsNews #TTP #TTPListicle #York
https://www.europesays.com/uk/90839/ IndyCar starting grid for Sonsio Grand Prix at Indianapolis Motor Speedway #Auto #AutoRacing #F1 #Formula1 #Formula1 #in #Indianapolis #IndianapolisMotorSpeedway #indycar #Know #Listicle #motor #MotorSports #News #Overall #OverallPositive #Positive #racing #scores #speedway #sport #SportScoresU0026Statistics #Sports #SportsNews #statistics #TTP #TTPListicle #TTPWhatWeKnow #u0026 #UK #UnitedKingdom #We #what
How come you deleted the tweet asking me to compare him to the legends to the list? Could it be because of this?
Tatum: 24.3 ppg
Kobe: 22.4
LeBron: 28.0
Parker: 18.9 ppg
KD: 28.9 ppg
Quick question, what's more impressive?
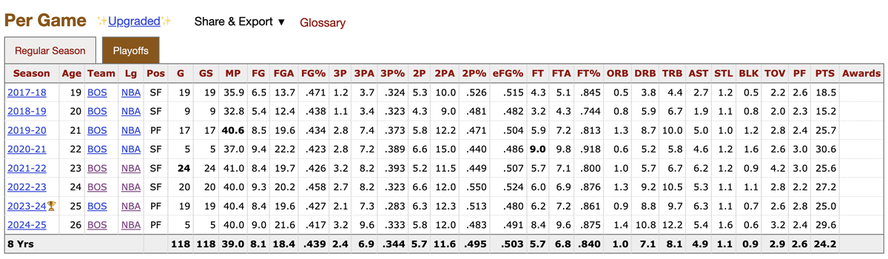
24.0 ppg in 73 playoff games (Murray)
24.2 ppg in 118 playoff games (Tatum)?
Not only that, he's been over 25 ppg since he was 21 years old. I get it, as a Sixers fan he's hurt you and you can't accept it #TTP https://x.com/SoJerZ_/status…
https://www.europesays.com/2033351/ Vatican says conclave to elect new pope will begin May 7; live updates #belief #blog #CatholicChurch #catholicism #city #Coverage #Francis #Know #live #LiveCoverage #Modular #ModularStory #Negative #News #Overall #OverallNegative #Pope #PopeFrancis #Religión #ReligionU0026Belief #Roman #RomanCatholicism #Rome #StatoDellaCittàDelVaticano #StatusCivitatisVaticanae #story #TTP #TTPLiveBlog #TTPWhatWeKnow #u0026 #Vatican #VaticanCity #VaticanCityState #Vaticano #We #what
Which stat would you prefer?
The one where he has the most made baskets in that spot since entering the league?
OR
The one where he's the most efficient on high volume with that shot in NBA history?
Your choice #TTP https://x.com/UPennSportsLvr…
Tech Transparency Project: Millions download covert Chinese VPNs https://www.telecomstechnews.com/news/tech-transparency-project-millions-download-covert-chinese-vpns/ #ttp #china #security #vpn #privacy #infosec #telecoms #connectivity #ios #android #mobile #tech #news #technology
#AIs as Trusted Third Parties
https://www.schneier.com/blog/archives/2025/03/ais-as-trusted-third-parties.html
>> A new #flashpoint is developing between #Pakistan and #Afghanistan as the former launched #extraterritorial strikes in #Paktika over claims that #PakistaniTaliban #TTP (ally of #AfghaniTaliban) use Afghan soil to launch attacks in Pakistan.
After #Pakistan, Now #Iran is at loggerheads with #Taliban!
Dam!
A new #flashpoint is developing between #Pakistan and #Afghanistan as the former launched #extraterritorial strikes in #Paktika over claims that #PakistaniTaliban #TTP (ally of #AfghaniTaliban) use Afghan soil to launch attacks in Pakistan.
Earlier, TTP attacked a Pakistani checkpoint and killed at least 16 Pakistani soldiers.
Afghanistan’s Defense Ministry said Saturday that its forces hit several points inside Pakistan in retaliation for deadly airstrikes last week.
https://apnews.com/article/afghanistan-pakistan-border-strikes-7dbd4af5dce9c2e9016d429253467312
Ah yes, but when it came to Joel Embiid you had a bit of a different stance. Color me shocked! #TTP https://x.com/mdschaeff/stat…
This #cybersecurity #TTP brought to you by the geniuses who, 20 years ago, used “or 2=2” in #sql injection attacks after WAFs began recognising and blocking “or 1=1”. #LLM #security
Read it and keep crying #TTP https://x.com/phillyguy23777…
He's only responsible for the greatest offense in NBA history. Keep crying #TTP https://x.com/phillyguy23777…
#ElonMusk will probably now sue Tech Transparency Project (#TTP)
https://www.engadget.com/x-let-terrorist-groups-pay-for-verification-report-says-201254824.html?src=rss
Another example of the same kind of #TTP was covered earlier today at #OBTS by the #Jamf threat research folks. The #RustBucket dropper, disguised as a custom "protected PDF reader" app, includes social engineering-flavored instructions on how to run the app: right-click to open. The attacker's story is that the app is so custom and secure it is unable to live on the #AppStore. Or to be notarized apparently, which triggers the #Gatekeeper warning thus necessitating the override instructions
Another example in the "pros" column for managing your users' ability to be tricked by this malicious actor tactic. `DisableOverride=True`, all day long.
https://www.youtube.com/live/9hjUmT031tc (Live, scroll back to about -5:21:08)
How is Pakistan dealing with threat emanating from Afghanistan? | Inside Story
Pakistan explosions: Dozens killed in two blasts